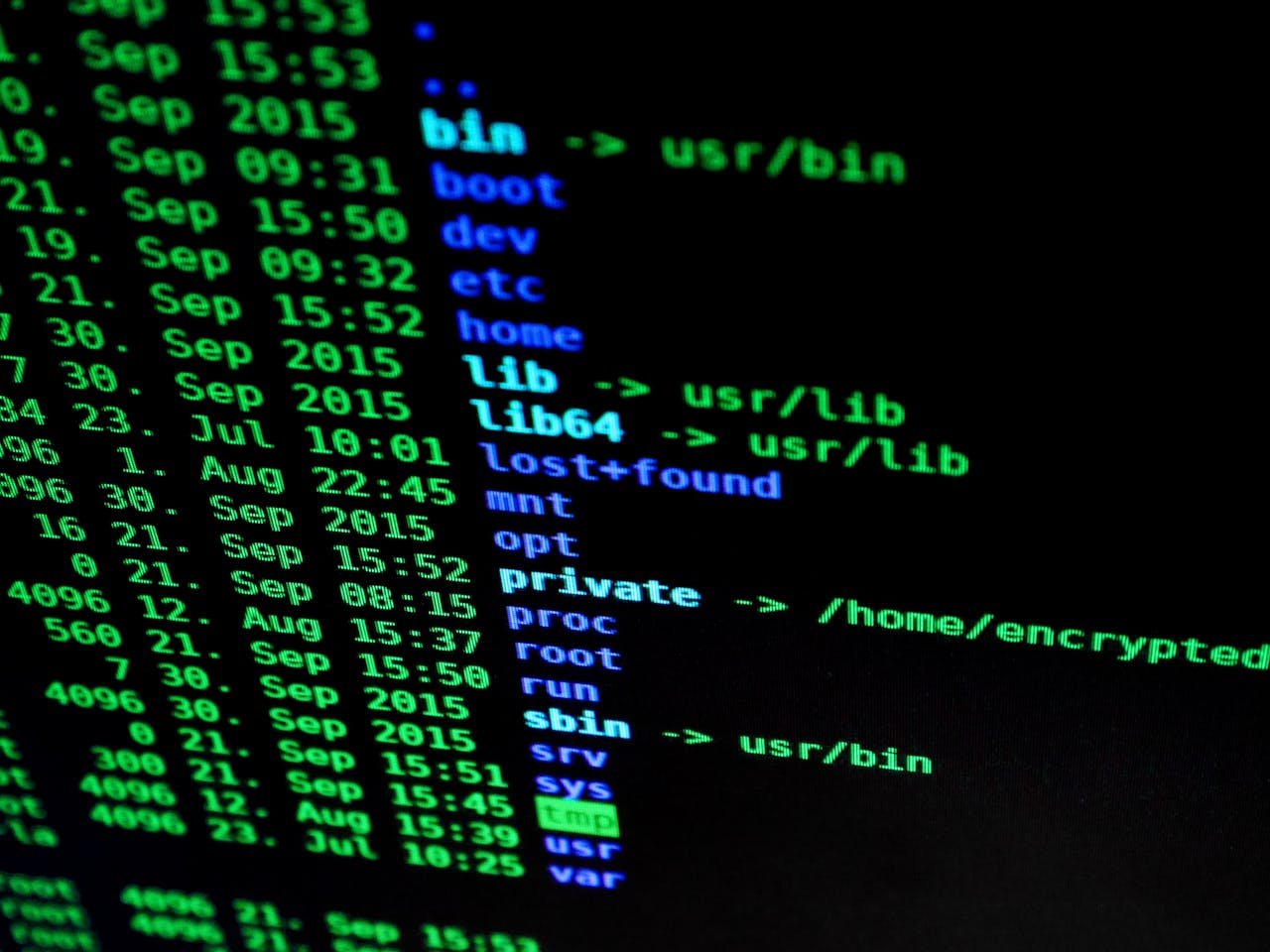
Comprehensive Cybersecurity Solutions
Protecting Your Business from Cyber Threats

01.
Vulnerability Assessments
Our Vulnerability Assessments involve a thorough evaluation of your IT infrastructure. By identifying potential weaknesses and security gaps, we provide actionable insights to remediate risks and strengthen your security posture, ensuring your organization is safeguarded against evolving cyber threats.
02.
Incident Response
Our Incident Response service equips your organization with the tools necessary to quickly identify, contain, and recover from cyber incidents. With a focus on minimizing damage, we offer expert guidance and support, enabling you to restore normal operations while protecting your reputation and ensuring regulatory compliance.

03.
Security Awareness Training
Our Security Awareness Training instills a culture of cybersecurity within your organization. Through engaging sessions, we equip your workforce with the knowledge to identify phishing attempts, malware, and other threats, reducing human error and fortifying your defenses against cyber attacks.
04.
Managed Security Services
With our Managed Security Services, we take on the responsibility of monitoring and managing your cybersecurity landscape. Our expert team works round the clock to detect and respond to threats, ensuring constant protection and compliance with industry standards while you focus on running your business.

Our Proven Process
A Seamless Approach to Cybersecurity
Assessment
We conduct thorough evaluations to understand your current cybersecurity posture.
Implementation
Our team deploys tailored strategies to enhance your security measures.
Monitoring
Continuous surveillance to detect and respond to threats in real time.
Take the First Step Towards Cyber Security Excellence
Contact us to learn how our customized solutions can protect your business from evolving cyber threats.